
Leaked documents reveal the secrets behind Graykey, the covert forensic tool used to unlock modern smartphones, exposing its struggles with Apple’s latest iOS updates.
Graykey is a forensic tool designed to unlock mobile devices and extract data, primarily used by law enforcement agencies and digital forensics experts. Developed by the secretive company Grayshift — now owned by Magnet Forensics — Graykey has earned a reputation for its ability to bypass smartphone security measures.
The tool helps law enforcement and forensic professionals in accessing locked mobile devices during criminal investigations. It breaks device encryption and security features to retrieve personal data like messages, photos, app data, and metadata.
Graykey supports Apple and Android devices, though its effectiveness varies depending on the specific hardware and software involved. Graykey’s capabilities and limitations, however, are rarely disclosed.
However, a leak of some Grayshift’s internal documents was recently reported on by 404 Media. According to the data, Graykey can only perform “partial” data retrieval from iPhones running iOS 18 and iOS 18.0.1.
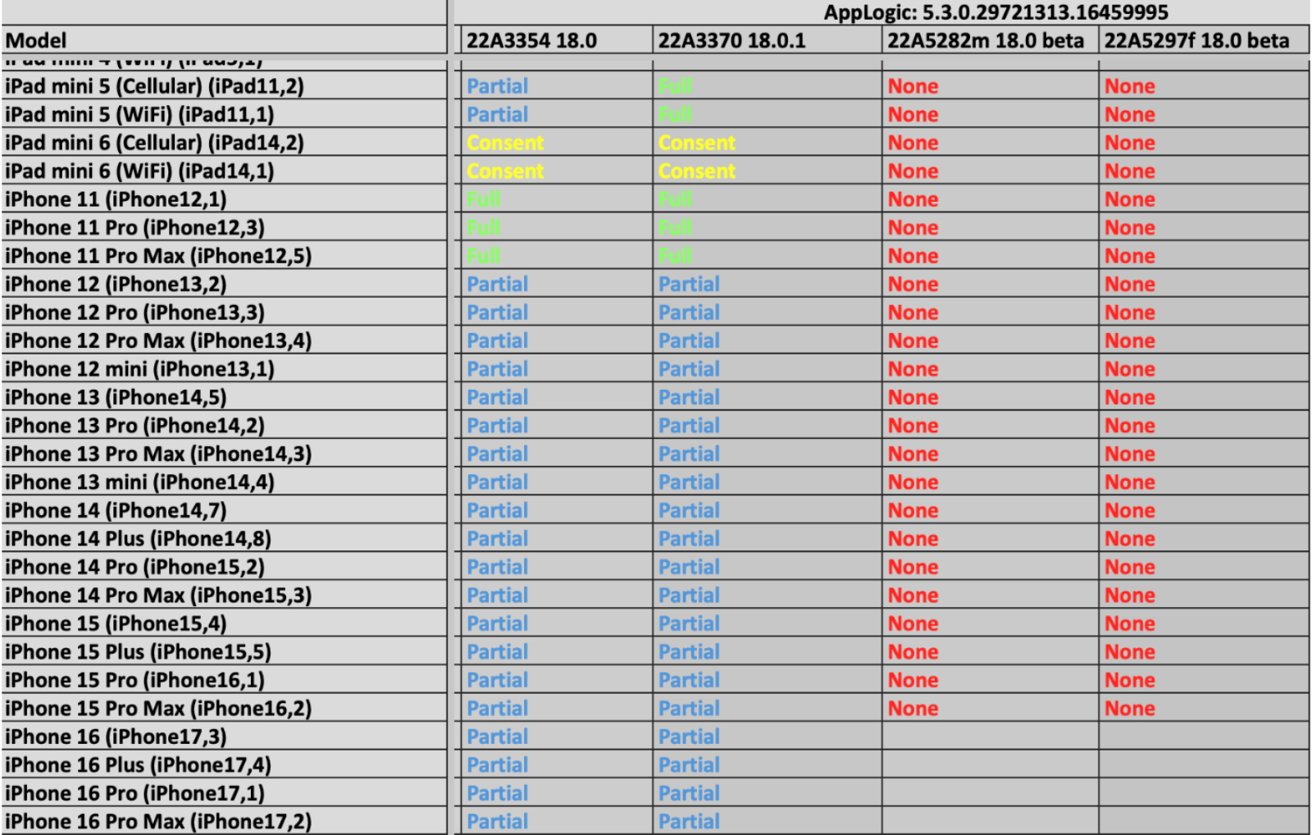
An image of a document detailing Graykey’s functionality with iPhones operating on iOS 18.0 and 18.0.1. Image credit: 404 Media
These versions were released in September and early October, respectively. A partial extraction likely includes unencrypted files and metadata, such as folder structures and file sizes, according to past reports.
Notably, Graykey struggles with beta versions of iOS 18.1. Under the latest update, the tool fails to extract any data, as per the documents.
Meanwhile, Graykey’s performance with Android phones varies, largely due to the diversity of devices and manufacturers. On Google’s Pixel lineup, Graykey can only partially access data from the latest Pixel 9 when in an “After First Unlock” (AFU) state — where the phone has been unlocked at least once since being powered on.
Andrew Garrett, CEO of Garrett Discovery, confirmed that the leaked documents align with Graykey’s known capabilities. Meanwhile, Magnet Forensics and Apple declined to comment on the leak.
Cat and mouse game
The leaked documents shed light on the ongoing battle between tech companies like Apple and forensic firms. Apple’s frequent security updates and features, including USB Restricted Mode and iPhone rebooting after inactivity, have made unauthorized access increasingly difficult.
In response, companies like Grayshift and Cellebrite continue to develop new exploits to bypass these safeguards. While tools like Graykey may lag behind new OS releases, historical trends suggest they often catch up eventually.
Forensic experts expect the cycle of vulnerabilities and patches to persist as Apple and Google continue fortifying their systems against unauthorized access.




