
Using Apple’s network security features.

Apple devices use many common internet security standards. Here’s what each of them does, and how to use them on your Mac, iPhone, or iPad.
In the networked world we live in, internet connectivity is ubiquitous.
Keeping network communications secure is one of the most important aspects of internet technology. Over the decades, several different standards have evolved to keep networks and devices secure.
In this article we’ll look at several of these standards, and how they relate to Apple devices.
IPsec, IKEv2, L2TP
Three key technologies are used for secure connections and VPNs: IPsec, IKEv2, and L2TP.
IPSec is a security standard which was born of early DARPA ARPANET research. It was later formalized by MIT, Motorola, and NIST.
IPSec is mostly used by VPNs, providing secure authentication, key exchange, encryption, and data integrity functions. If you’ve ever installed VPN software on one of your Apple devices, you’ve used IPSec.
It is considered a “Layer 3” protocol which sits atop Layer 2 protocols, which we’ll see in a moment.
IKEv2 is the Internet Key Exchange protocol. There are three versions this protocol: IKE, IKEv1, and IKEv2.
It is used in IPSec and by DNS to create and exchange secure key pairs during connections. Shared keys are part of Public Key Infrastructure (PKI) which eliminates the need for passwords.
IKE is based on two earlier protocols: The Oakley protocol and ISAKMP. These protocols came out of efforts in the late 1990’s to secure internet connections when it became clear early internet communications were insecure in many instances.
The Oakley protocol uses the now-famous Diffie-Helman Key Exchange algorithm to securely exchange keys for encryption.

Network security server room
ISAKMP is a key exchange framework that provides a security association and keys to be used by key exchange protocols such as IKE. Cisco adopted both the Oakley and ISAKMP protocols for use in most of its VPN and router products.
There are other key exchange protocols, such as Kerberized Internet Negotiation of Keys (KINK) and SKEME.
L2TP, or Layer 2 Tunneling Protocol is a tunneling protocol used for control messages during network communication. L2TP doesn’t secure or encrypt data or content itself, it only encrypts the control signals used in connections.
This protocol was formalized in 1999 in the RFC 2661 specification which was formed as a result of Cisco’s L2F protocol and Microsoft’s PPTP protocol. It also uses the User Datagram Protocol (UDP) during packet transmission.
UDP has the main advantage of being an acknowledgment-free broadcast protocol, for which listeners wait on a certain port for information without having to reply to the sender.
L2TP came about as a need for security for PPP (Point-To-Point Protocol) when dial-up modems were still in widespread use. Data packets can be transmitted over a Layer 2 tunnel by using one of the other additional encrypted protocols.
Secure tunneling ensures any data traveling in the tunnel is encrypted and controlled between only two points. This makes replay and man-in-the-middle attacks difficult for attackers to execute.
Since the internet spans the globe, security is important.
L2TP is used mostly in corporate VPNs for secure access.
Many VPN apps are available for Apple devices, via the App Store. Most Apple operating systems also provide built-in features for easily adding VPN profiles to devices.
IPsec, IKEv2, and L2TP operate mostly behind the scenes, and unless there’s some specific setting you need to change, you’ll usually never need to bother yourself with them.
TLS, SSL, and X.509 certs
When the web first went mainstream in the late 1990s, it quickly became apparent that all web communication needed to be encrypted. All so that data couldn’t be intercepted and listened to between browsers and servers.
As a result Secure Sockets Layer (SSL) was developed. Now called Transport Layer Security, this protocol encrypts most traffic between web browsers and servers.
The “s” in “https” stands for “secure” – and indicates that you are browsing a website via a secure connection.
SSL/TLS can also be used in some secure email communications. TLS was also proposed in 1999 and has undergone three revisions, the current version of which is TLS 1.3.
SSL was originally developed in 1994 for the first versions of Netscape’s Navigator browser, which today has morphed into Mozilla Firefox. There is also a Datagram Transport Layer Security (DTLS) protocol.
TLS uses X.509 certificates to exchange information using encryption and encrypted handshakes. Once the handshake completes, the server usually provides the client app with a certificate so sever can be trusted.
X.509 certificates allow a client app to verify the authenticity of the server, so that impersonation attacks can’t work. The X.509 standard is defined in RFC 5280 by the International Telecommunications Union (ITU).
The major benefit of TLS is that it prevents anyone who might be listening in on the data exchange from being able to read the data in the clear. All due to it being encrypted.
In most cases, modern Apple devices and most software running on Apple devices automatically know how to use TLS, so you shouldn’t need to worry about it. As long as you use an “https” connection when browsing the web, TLS is automatic.
Some email client apps such as Mozilla Thunderbird allow you to specify TLS/SSL as the communication security standard:
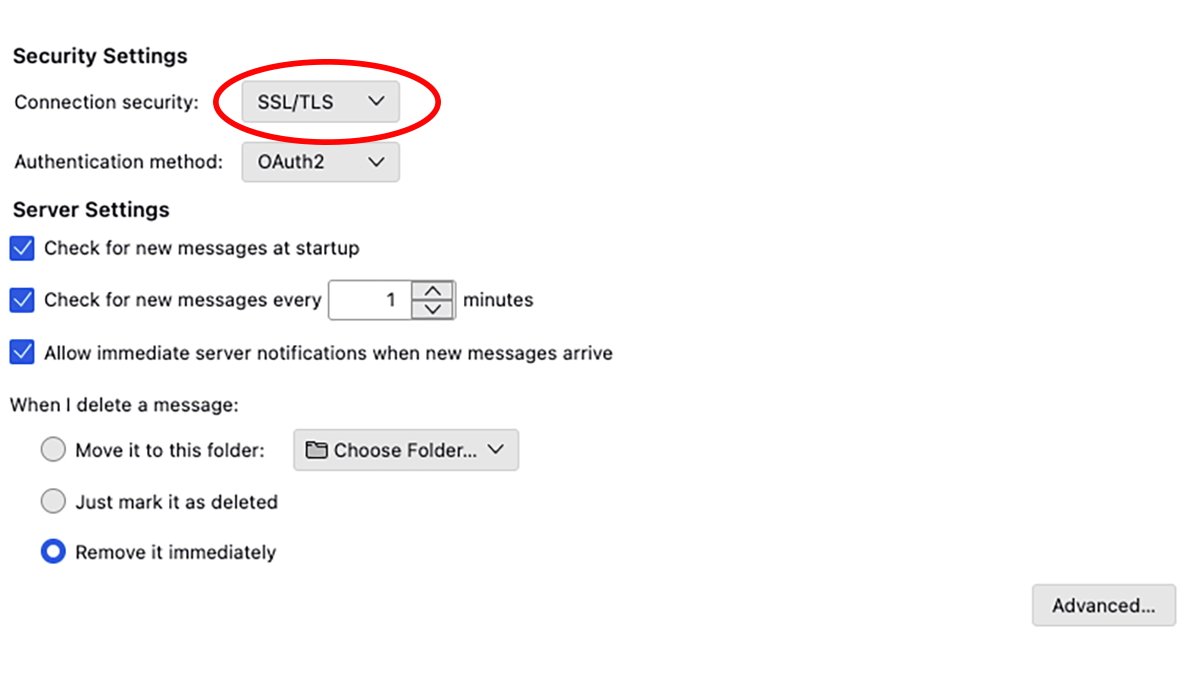
Mozilla Thunderbird’s TLS security setting interface.
WPA/WPA2/WPA3 Enterprise and 802.1X
When WiFi networking first appeared at the end of the last century, a new security standard, WEP (Wired Equivalency Privacy) was developed to allow wireless networks to connect to other devices securely.
WEP had serious security flaws, and in response, Wi-Fi Protected Access (WPA) was produced. This protocol has undergone three revisions since the early 2000s, with the current version being WPA3.
Most modern WiFi devices, including Apple’s devices, provide WEP3 for connections.
Both Apple’s WiFi and Ethernet devices also provide for connections that use another security protocol called 802.1X. This protocol is part of the 802 network standard as defined by IEEE, which covers both WiFi and Ethernet wired networks.
802.1X prevents a type of network attack known as Hardware Addition, where a malicious device is used to attach to a network and perform hacking activities. For example, a small computer like a Raspberry Pi plugged into a spare network port.
Via the use of an authentication server, 802.1X can usually thwart such attacks by authenticating the user via WiFi, LAN, or WAN.
In today’s world of devices everywhere, Hardware Addition attacks are much more common than they used to be.
WPA is no longer supported by modem versions of Apple’s operating systems, so in most cases, you’ll want to use WPA2, WPA3, or some variant thereof.
Login Window Mode (LWM) is a way to connect to a secure network from the Mac’s login window if the network supports Directory Services.
In order to use LWM, you need a connection to an Active Directory or Open Directory server. You will also need an installed Mac network configuration profile which enables LWM for the network you’re trying to connect to.
Once configured, at the Mac Login Window, select Other from the list of users, then enter your Directory Services user name and password. From the popup menu, select the network interface you want to connect on (WiFi or Ethernet).
Active Directory and Open Directory are technologies that allow user information and credentials to be stored on a central server for authentication.
In most cases, Apple has made network security seamless so you usually won’t need to worry about it. The above technologies are mostly all part of web or internet standards, and in most software their use is automatic.




